Offensive Security Certified Expert (OSCE) – No pain, no gain!

0x00 – What? Why? Overview
After completing the previous Offensive Security course, Penetration testing With Kali, Cracking The Perimeter (CTP) was a natural choice and continued from where the previous course left off. Goal of the course was to cover more advanced methods and techniques in penetration testing. As it states in Offensive Securitys web page, there is one purpose for the course: how to bypass security. It gives a wide variety of skills for seeing what kind of attack methods hackers can use, what tools they use and how little is needed to crack a server or even bypass a firewall or antivirus softwares. You learn the methods hackers use to exploit vulnerable systems.
0x01 – Signing to course
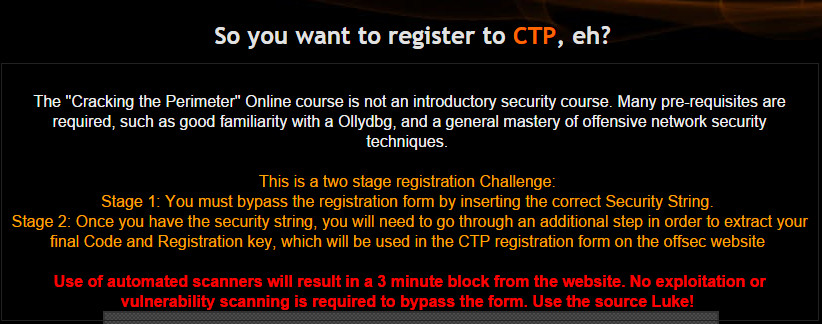
Offensive Security has standards and it can also be seen from their attitude towards possible candidates to the CTP course. While they could harvest money from all people and book the course for anyone who is interested, they have setup a hacking challenge that has to be solved before even signing to the course! Pre-registration challenge is located at http://www.fc4.me/ site. If student candidate is able to complete the challenge (without help!), he has the needed pre-requisities for the course. Skills that are very useful and/or help with the course are programming background, creative thinking, good nerves, python and famialirity with debuggers (e.g. Immunity Debugger, Ollydbg, IDA).
0x02 – Course overview
Foreword: Course material is a bit outdated, but by no means it is obsolete. Course gives students basics in exploit development. Althought the course is from the side of offensive security, student can use knowledge from course to good or evil.
When the course starts, student gets following items via email (links to them):
- Course PDF.
- Lab videos.
- VPN credentials and configuration.
- Access to lab servers.
- Access to to student panel, so it’s possible to revert the servers back to their original states.
- Backtrack VM image.
Topics covered in the course are:
- Web application angle
- Two real world scenarios, consisting of XSS, LFI to remote code execution. A bit like PWK course, but nonetheless, it shows a few interesting methods.
- Backdoor angle
- Methods to inject backdoors in PE executables and some basic AV bypassing techniques. This is where the fun part begins and you start using debugger.
- Advanced Exploitation Techniques
- Bypass ASLR, egghunters etc.
- The 0Day angle
- Finding new vulns, fuzzing, etc.
- The Networking angle
- Interesting real world scenario with network devices.
As in PWK course, lab manual and videos nicely complement each other. Compared to PWK labs, CTP labs are way different. You don’t have as many servers as targets, but you jump around in the victim servers memory until you head spins and your mind is filled with HEX, registers and shellcode etc.etc. Exploit development section in PWK is just a scratch in the surface of exploit development and in CTP you’ll get a way more comprehensive understanding of exploit development process and methods. You will jump around a single computers memory, from corner to corner (while doing all kind of acrobatics) until you are exceptionally familiar with debugger.
I did only one part of the whole course with Backtrack, for the rest I used Kali 2.0. I used Backtrack to generate one shellcode, since the shellcode I generated with Kali 2.0 (with msfpayload) didn’t work in the exercise that it was used. Offensive Security suggests that Backtrack should be used to get most streamlined experience from the course.
To get most from the course, students should push themselves further to learn the sections fully and comprehensively by doing the exercises a bit differently and experimenting methods that are not in course material (my opinion). Basicly, if you lack skills in some topics, you should do a lot more research on the subject. I for one, did more than enough research and I went a bit further in each exercise than was necessary. It never hurts to know more than is necessary, right?
Material (lab+Videos) have some gaps and as always, there is the Offensive Security ‘curveball’ present in most of the exercises. You’re discouraged to copy solutions from lab materials and that should be obvious. As some people say, the course material is a bit outdated, but still, it gives you the basics of exploit development. The skills taught give you more than enough knowledge to enhance your skills.
0x03 – The Exam
The Exam. Well, first of all, the exam was a bit longer than the one in PWK course. CTP course exam for OSCE certification is 48 hours and after that time, students have to submit the report back to Offensive Security in 24h hours. When the exam starts, student will get email from Offensive Security with…
- VPN connection details to the Exam network.
- Exam manual with questions.
- Lab control panel with more than enough reverts.
Exam consists of a number of tasks that are rated differently and you should have about 85 % of the points to pass the exam. That means almost every task should be completed. Much detail about the exam can’t be revealed, but it was pretty brutal. Everything to complete the exam tasks are in course materials, but creative thinking is needed to pass. The exam is pretty brutal and students will probably learn as much doing the exam as they did while doing the lab exercises.
Tips for exam:
- Remember to get a good nights sleep to recharge and to be at top shape mentally.
- Make a plan. A good plan.
- If you get stuck, take a step back and take a break. Go for a walk or something and then try to think what you’re doing wrong, what are your options
- Oh, did I mention that you should get some proper sleep before you go at it? And of course while doing the exam.
0x04 – Final thoughts
Skills that you have, but not limited, after the course include exploit development, fuzzing, even more ”Try Harder!” mindset than before. You also have to be prepared to do some of your own research to hone your skills even more and I recommend it.
Few times in my life I have felt like my skills are not good enough (without bragging) or I’m completely lost that what I even should try to research. It was frustrating. But I used the ”Try Harder!” method and tried harder.
I had 60 days of labtime and I did the course in the evenings after work. Course takes a lot of time and you should be ready to spend a lot of time studying, doing exercises etc. At least if you’re not familiar with exploit development.
Big thanks go to my wife and family for support and understanding my need of time (a lot of time) to study.